How To Access The BIOS On A Windows 8 Computer
Among the many changes coming with Windows 8 and new computers designed for it is a change in the way we access our computers’ BIOS. No longer do we press a certain key during the boot process to reveal the BIOS – instead, an option to access the BIOS is located in Windows 8’s boot options menu.
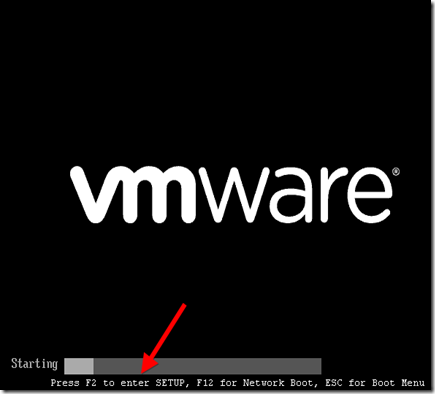
Traditionally, computers displayed a message like “Press F2 to enter setup” at the beginning of the boot process. Pressing this key entered the computer’s BIOS. However, Windows 8 hardware uses the UEFI replacement for the traditional BIOS, like Macs do. Some solid-state drive-equipped Windows 8 PCs boot so fast that you’d only have a 200 millisecond (that’s 0.2 seconds) window of opportunity to press the key combination.
Windows 8 Hardware vs. Old Computers With Windows 8
Note that this new method only applies if you purchased a new computer with Windows 8 preinstalled – these will use UEFI. However, if you’ve installed Windows 8 on an existing computer that uses the legacy BIOS system, you’ll access the BIOS in the same way as always by pressing the key that appears during your boot process.
This key is often F2 or Delete, but it can also be other keys. The exact key depends on your computer – if you don’t see the appropriate key displayed on your screen during the boot-up process, consult your computer’s manual.
Accessing Boot Options
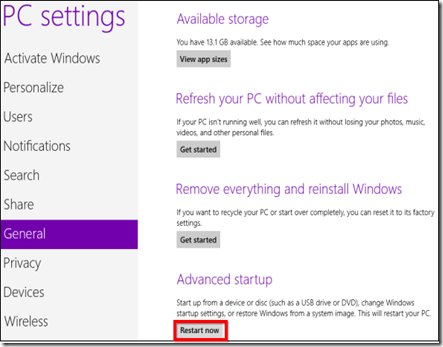
There are several ways to access Windows 8’s boot options menu. The easiest one to find is in the PC Settings application – press WinKey+C to reveal the Charms bar, click Settings, and select Change PC settings to access it.
In the PC Settings application, select the General category and click the Restart now button under Advanced startup. Your computer will restart and you’ll enter the Windows 8s boot options menu, where you can access the UEFI BIOS and change other settings.
In more updated versions of windows 8 (like 8.1), the Advanced startup has moved:
Windows Key+C > Settings > Change PC settings > Update and recovery > Recovery > Advanced startup + Restart now
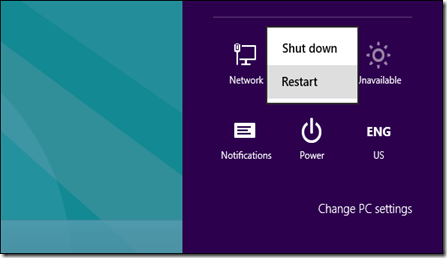
You can also hold Shift while clicking Restart in the Shut Down menu to restart your computer into the boot options menu. This is a quick way to restart into the boot options menu, as you can access the Shut Down button from the Charms anywhere on your system.
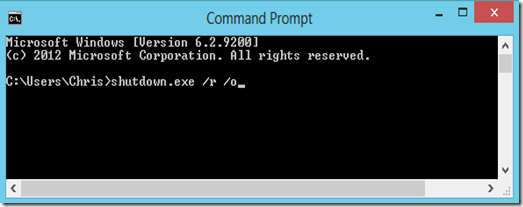
Command-line geeks will be happy to know they can run a special shutdown.exe command in a Command Prompt window to restart their computer directly into the boot options menu:
Shutdown.exe /r /o
Accessing UEFI BIOS
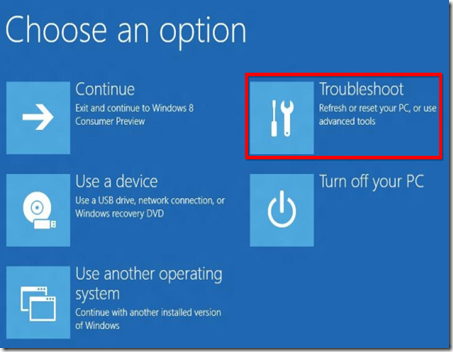
The boot options menu has been designed to integrate some commonly used options that people went into the BIOS for. For example, if you want to boot your computer off a USB drive, DVD or CD, or another device, you can click the Use a device tile in the boot options menu and select the device you want to boot from.
If you’re just here to access your computer’s UEFI BIOS, click the Troubleshoot tile.
This will reveal an Advanced Options screen with a variety of tools – the UEFI Firmware Settings tile will take you to your computer’s BIOS. (On UEFI, which stands for “Unified Extensible Firmware Interface”, the firmware settings menu is equivalent to a traditional PC’s BIOS.)
If you don’t see the UEFI Firmware Settings tile here, your computer doesn’t use UEFI. You’ll need to access the BIOS in the traditional way, by pressing a specific key during the boot-up process. See the first section above for more information.
If there’s an error booting Windows, you won’t be locked out of the BIOS — the boot options screen will appear when you start your computer. From here, you can repair Windows or enter your BIOS.
Why the Change?
While this may be slightly inconvenient, as there’s no way to access the BIOS in normal use without booting into Windows first, it’s surely necessary. Microsoft’s blog post about this on the Building Windows 8 blog describes how this new system came to be. With the increased boot speed, some systems had a less than 200 millisecond window of opportunity to press a key. Even the best key-tappers at Microsoft could only press a key once every 250ms — to access the BIOS, frantic tapping, luck, and several compuer reboots were all necessary.
This also brings some much-needed consistency to Windows 8 computers — they’ll all have a consistent way of accessing the BIOS. Currently, different computers use different keys at start-up.
While Windows 8 may have some questionable design decisions that some people will dislike, this shouldn’t be one of them. The new method of accessing the BIOS is necessary and well-implemented.
Taken From: http://www.makeuseof.com/tag/how-to-access-the-bios-on-a-windows-8-computer/ (By Chris Hoffman)